【President diary】EC-CUBE4.2.1
Today, new version of EC-CUBE that strengthened security functions such as vulnerability was released.
https://www.ec-cube.net/news/detail.php?news_id=435
Two of our members were cooperating to the debug. If you know already the members, you can see who they are on the website above because their real names are used for IDs.
When I see news about leaking of credit card information, I always check the company’s websites whether the problems are not about EC-CUBE. These days, there were many of leaking cases not EC-CUBE websites. The user’s guide of website that leaked this month says “There is no need to worry since the data is stored in ASP.”, I was surprised even the famous ASP has occurred such problems. However, there is no information of vulnerability on the website, I guess the case might cause operation mistake such as stealing admin password, somebody coded for information theft.
One of good points of EC-CUBE is obvious notification of vulnerability information. You can see all vulnerabilities found ever and judge how it is dangerous or safe. In case of ASP, they do not have to publish these information since the operating company fix them, but it is in “black box” how they have fixed ever.
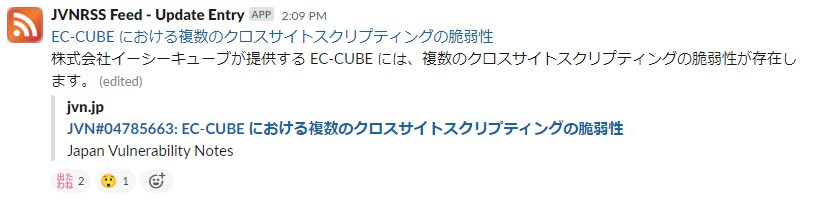
Vulnerability of EC-CUBE is notified by IPA and so on. Our company’s system always monitors by setting to get notifications of JVNRSS to SLACK, like this↓
When a patch is released, our e-commerce team prepares for emergency in order to apply to supporting e-commerce website. It was low risk for this release, but there comes tense atmosphere when it is high risk. Even if EC-CUBE issues a patch, it is meaningless unless it is applied. You should apply the patch as soon as the release is announced.
EC-CUBE has enhanced security settings these years. Hope you’ll check more details from the official websites below.

